Common Types Of Trojan Malware, From A to Z
🔰
Common Types Of Trojan Malware, From A to Z 🔰🔅
🔻━━━━━━━━━━━━━
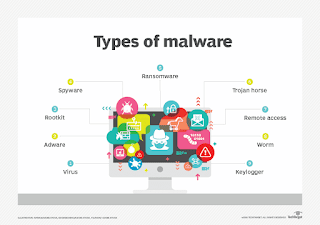
Here’s a look at some of the most common types of Trojan malware, including their names and what they do on your computer:
Backdoor Trojan
🔻━━━━━━━━━━━━━
This Trojan can create a “backdoor” on your computer. It lets an attacker access your computer and control it. Your data can be downloaded by a third party and stolen. Or more malware can be uploaded to your device.
Distributed Denial of Service (DDoS) attack Trojan
🔻━━━━━━━━━━━━━
This Trojan performs DDoS attacks. The idea is to take down a network by flooding it with traffic. That traffic comes from your infected computer and others.
Downloader Trojan
🔻━━━━━━━━━━━━━
This Trojan targets your already-infected computer. It downloads and installs new versions of malicious programs. These can include Trojans and adware.
Fake AV Trojan
🔻━━━━━━━━━━━━━
This Trojan behaves like antivirus software, but demands money from you to detect and remove threats, whether they’re real or fake.
Game-thief Trojan
🔻━━━━━━━━━━━━━
The losers here may be online gamers. This Trojan seeks to steal their account information.
Infostealer Trojan
🔻━━━━━━━━━━━━━
As it sounds, this Trojan is after data on your infected computer.
Mailfinder Trojan
🔻━━━━━━━━━━━━━
This Trojan seeks to steal the email addresses you’ve accumulated on your device.
Ransom Trojan
🔻━━━━━━━━━━━━━
This Trojan seeks a ransom to undo damage it has done to your computer. This can include blocking your data or impairing your computer’s performance.
Remote Access Trojan
🔻━━━━━━━━━━━━━
This Trojan can give an attacker full control over your computer via a remote network connection. Its uses include stealing your information or spying on you.
Rootkit Trojan
🔻━━━━━━━━━━━━━
A rootkit aims to hide or obscure an object on your infected computer. The idea? To extend the time a malicious program runs on your device.
SMS Trojan
🔻━━━━━━━━━━━━━
This type of Trojan infects your mobile device and can send and intercept text messages. Texts to premium-rate numbers can drive up your phone costs.
Trojan banker
🔻━━━━━━━━━━━━━
This Trojan takes aim at your financial accounts. It’s designed to steal your account information for all the things you do online. That includes banking, credit card, and bill pay data.
Trojan IM
🔻━━━━━━━━━━━━━
This Trojan targets instant messaging. It steals your logins and passwords on IM platforms.
That’s just a sample. There are a lot more.
Common Types Of Trojan Malware, From A to Z 🔰🔅
🔻━━━━━━━━━━━━━
Here’s a look at some of the most common types of Trojan malware, including their names and what they do on your computer:
Backdoor Trojan
🔻━━━━━━━━━━━━━
This Trojan can create a “backdoor” on your computer. It lets an attacker access your computer and control it. Your data can be downloaded by a third party and stolen. Or more malware can be uploaded to your device.
Distributed Denial of Service (DDoS) attack Trojan
🔻━━━━━━━━━━━━━
This Trojan performs DDoS attacks. The idea is to take down a network by flooding it with traffic. That traffic comes from your infected computer and others.
Downloader Trojan
🔻━━━━━━━━━━━━━
This Trojan targets your already-infected computer. It downloads and installs new versions of malicious programs. These can include Trojans and adware.
Fake AV Trojan
🔻━━━━━━━━━━━━━
This Trojan behaves like antivirus software, but demands money from you to detect and remove threats, whether they’re real or fake.
Game-thief Trojan
🔻━━━━━━━━━━━━━
The losers here may be online gamers. This Trojan seeks to steal their account information.
Infostealer Trojan
🔻━━━━━━━━━━━━━
As it sounds, this Trojan is after data on your infected computer.
Mailfinder Trojan
🔻━━━━━━━━━━━━━
This Trojan seeks to steal the email addresses you’ve accumulated on your device.
Ransom Trojan
🔻━━━━━━━━━━━━━
This Trojan seeks a ransom to undo damage it has done to your computer. This can include blocking your data or impairing your computer’s performance.
Remote Access Trojan
🔻━━━━━━━━━━━━━
This Trojan can give an attacker full control over your computer via a remote network connection. Its uses include stealing your information or spying on you.
Rootkit Trojan
🔻━━━━━━━━━━━━━
A rootkit aims to hide or obscure an object on your infected computer. The idea? To extend the time a malicious program runs on your device.
SMS Trojan
🔻━━━━━━━━━━━━━
This type of Trojan infects your mobile device and can send and intercept text messages. Texts to premium-rate numbers can drive up your phone costs.
Trojan banker
🔻━━━━━━━━━━━━━
This Trojan takes aim at your financial accounts. It’s designed to steal your account information for all the things you do online. That includes banking, credit card, and bill pay data.
Trojan IM
🔻━━━━━━━━━━━━━
This Trojan targets instant messaging. It steals your logins and passwords on IM platforms.
That’s just a sample. There are a lot more.


Comments
Post a Comment